Description
Description
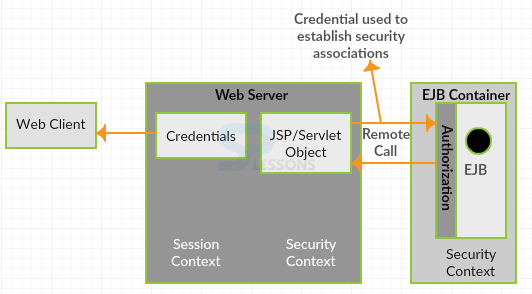
JSP Security - As of now Splessons covered everything related to JSP technology such as form creation, database access, filters, debugging and also developing small applications like forms, but every web application developed by JSP, Servlet needs the security, without security it will not be worth.Following are the Several levels of authentications.
- Role based authentication.
- Form based authentication.
 Conceptual
Figure
Conceptual
Figure
 Description
Description
The affirmation component in the servlet determination utilizes the strategy called role based security. This thought is that instead of constraining assets at the client level, we make parts and confine the assets by role. One can keep different roles in file tomcat-users.xml as follows.
[java]
<?xml version='1.0' encoding='utf-8'?> <tomcat-users> <role rolename="tomcat"/> <role rolename="role1"/> <role rolename="manager"/> <role rolename="admin"/> <user username="tomcat" password="tomcat" roles="tomcat"/> <user username="role1" password="tomcat" roles="role1"/> <user username="both" password="tomcat" roles="tomcat,manager"/> <user username="admin" password="secret" roles="admin,role1"/> </tomcat-users
[/java]
The above file determines mapping between different fields such as user name, password and role where user may have multiple roles. By using in web.xml role based security limitations will be placed in different web applications.Following is the sample web.xml file.
[xml]
<web-app>
...
<security-constraint>
<web-resource-collection>
<web-resource-name>
SecuredBookSite
</web-resource-name>
<url-pattern>/secured/*</url-pattern>
<http-method>GET</http-method>
<http-method>POST</http-method>
</web-resource-collection>
<auth-constraint>
<description>
Let only managers use this app
</description>
<role-name>manager</role-name>
</auth-constraint>
</security-constraint>
<security-role>
<role-name>manager</role-name>
</security-role>
<login-config>
<auth-method>BASIC</auth-method>
</login-config>
...
</web-app>
[/xml]
 Description
Description
While using form authentication method developer supposed to create fields to enter the credentials. Following is the sample code of JSP form.
[java]<html>
<body bgcolor="#ffffff">
<form method="POST" action="j_security_check">
<table border="0">
<tr>
<td>Login</td>
<td><input type="text" name="j_username"></td>
</tr>
<tr>
<td>Password</td>
<td><input type="password" name="j_password"></td>
</tr>
</table>
<input type="submit" value="Login!">
</center>
</form>
</body>
</html>[/java]
Where form tag must be "j_security_check" and element fields should be "j_username" and "j_password" and developer has to modify tag to specify auth-method as FORM:
[java]
<web-app>
...
<security-constraint>
<web-resource-collection>
<web-resource-name>
SecuredBookSite
</web-resource-name>
<url-pattern>/secured/*</url-pattern>
<http-method>GET</http-method>
<http-method>POST</http-method>
</web-resource-collection>
<auth-constraint>
<description>
Let only managers use this app
</description>
<role-name>manager</role-name>
</auth-constraint>
</security-constraint>
<security-role>
<role-name>manager</role-name>
</security-role>
<login-config>
<auth-method>FORM</auth-method>
<form-login-config>
<form-login-page>/login.jsp</form-login-page>
<form-error-page>/error.jsp</form-error-page>
</form-login-config>
</login-config>
...
</web-app>
[/java]
Here server maintains the sessions to recognize the authorized persons, cookies and session will play major role in the security mechanism.
 Methods
Methods
Following are the programmatic security methods in JSP and Servlet.
String getAuthType():To represent the identity of the authentication to protect servlet.
boolean isUserInRole(java.lang.String role):To return boolean values.
String getProtocol():represents the protocol to send data
boolean isSecure():Returns a boolean value representing if the request was created using HTTPS.
Principle getUserPrinciple():results a java.security.Principle object that contains the name of the current authenticated user.
 Key Points
Key Points
- JSP Security - JAVA security technology will have set of API'S, algorithms, tools.
- JSP Security - RBAC stands for Role based access control.
- A security constraint is utilized to describe the authentication privileges