Description
Description
Each Oracle 12c Administration database contain entire privileges to access the server database and can administer it. Because oracle database system is very huge and contains many users, and more over it is not a single user work. In that situation there is a group of data base administrators and can distribute the responsibility.
A following are the tasks that the Oracle 12C Administration is responsible for:
- Upgrading and installing the oracle application tools and oracle server
- Planning future storage requirements and allocating frame work storage for the database system
- Altering the structure of the database
- Maintaining the security system and registering the database users
- Monitoring and controlling the client access to the database
- When the client application develop the design phase,create primary objects in it
- Oracle license agreement compliance should be ensured
- Restoring and backing up the database
- Managing archived data on tapes
- For any technical issues contact oracle corporation
- Recovery and backup of information from the database
 Description
Description
The Oracle 12C Administration database users are
The oracle database 12c administrators contain one or more security officers. And a user will be enrolled by a security officers and can monitor, control and access user to the database and can handle entire security system. As a database administrator, one might not be responsible for these duties if different security officer site is operated.
Application developer implements and designs the database applications. And the task includes in these responsiblities are
One or more network administrators will be assigned for some site. All the oracle networking products will be administer by network administrator, like Oracle Net Services.
One or more application administrators will be assigned by oracle site to administrate a particular application.And each and every application contain it's own oracle administrators.
Through applications or utilities these database users will interacts with the database.The roles and responsibilities include for a typical users are
- Security officers
- Application developers
- Network administrators
- Application administrators
- Database users
- The structure of the database is design for an application
- Developing and designing the database application
- Calculating the storage specification for an application
- For an application modifying the structure of the database
- During the development phase the application should be tuned
- Application security measures should be established
- Creating,deleting and altering the data
- Preparing applications from the informations
 Description
Description
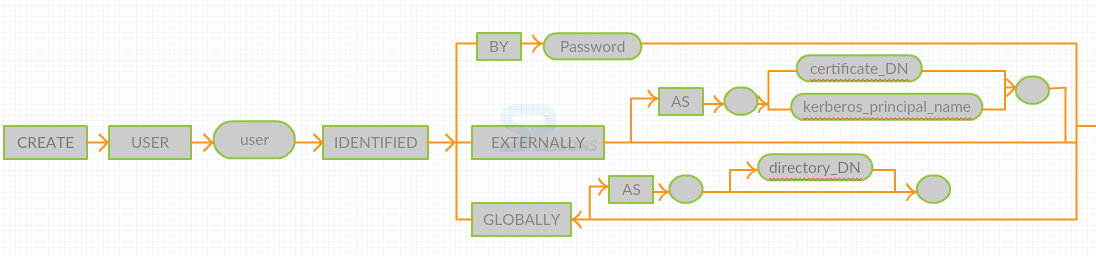
Create user is used to configure and create users in the database, through which the user can log into the database and an establish mutual connection between user and oracle database.
The statement can be issued in an clustered oracle automatic storage engagement to maintain password and user combination between the files that includes the current nodes containing the oracle ASM instance. All the oracle ASM instance nodes uses this statements to upgrade it's own individual password files. The ORAPWD utility can create the password by itself. Through application server or by proxy application.
Create user system privileges should be contain in the database. The create user statement is used to create a user, and contain the user privileges domain is empty. For logging into the oracle database, create session system privilege should be contained for a user.Hence after creating a user, you should grant the user for create session system privileges. Only authentication user as system can issue the command to alter the oracle ASM instance password file.
 Description
Description
Predefined users and roles includes 2 process i.e, allowing only certain clients to access and implementing various limits on clients for accessing.
The restrictions issued on client can be applied on objects like table rows,table columns and schemas. To run a particular sql statement must be implemented by a client privilege or another client is responsible for accessing the object, that run pl/sql package. All this privileges are predefined for oracle database. User is responsible for creating the roles for including other privileges or other different roles. And granting all this privileges to clients includes the following facilities and can classified into different categories.
In the database these privileges perform standard administrator tasks and can restrict them for trusted clients only and includes the following tasks like
- System privileges
- Roles
- Object privileges
- Table privileges
- View privileges
- Managing system privileges
- Managing administrative privileges
- Managing locally and commonly privileges for granted
- Managing local and common roles
- Managing roles of clients
 Description
Description
Operating system authentication means checking the identity of a particular client, who needs to access the data or view the data and applications.
For further interaction a mutual or trusted relationship should be established between these processes. And enables accountability for maintaining a specific identity and access links. Authorization process starts after authentication process and can allow or make some restrictions to access the permitted data entity.
Based on this oracle database can authenticate both database and non database clients. And similar authentication is used for all the database clients, but only single database instance will be allowed by oracle database for all this methods. For database administration a specific authentication process should be performed by oracle database, as it will perform special database operations and can encrypts passwords while performing security network authentications. The configuring privileges and role authorization process will be process under this authorization and can allow access permissions for this entities.
 Key Points
Key Points
- Oracle 12c Administration - Contain entire entire privileges to access the server database.
- Users in oracle 12c and roles - contain different types of database users and function accordingly.
- Creating users - Is used for configure and create users in the database.
- Predefined users and roles - Allowing only certain clients to access and implement various limits for accessing.
- Operating system authentication - Means checking the identity of particular such as username and password.