Description
Description
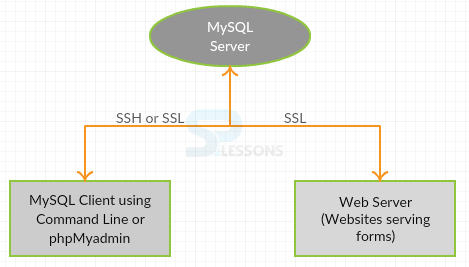
Control Access Lists are used in MySQL for each and every query operations and connections, that are a part of security for accessing the database accounts. There is additionally bolster for SSL-encoded associations among MySQL servers and MySQL users. A significant number of the ideas performed are not particular to only MySQL database and the same general thoughts apply to all the functions.
 Description
Description
The following steps explain some of the key instructions related to MySQL Security related to database.
- While performing the installation of MySQL database every records ought to be keep up legitimately and ought not unveil to anybody.
- To get to the MySQL database tables the root account assumes a key parts.
- MySQL uses revoke and grant privileges for accessing all the necessary controls that are related to the database.
- MySQL database passwords ought to be in clear content and contains the qualities that are a part of hash.
- Execute strings and tcpdumps functions and check the information in the database are decoded are not.
- Applications performed in MySQL ought not believe any information listed through clients, and ought to be composed utilizing legitimate cautious programming strategies.
- From the web, the information ought not be transmitted in plain content. This data is open to everybody who has room schedule-wise and capacity to block it and use it for their own particular purposes. Rather, utilize an encoded convention. For example, SSH or SSL. MySQL bolsters interior SSL associations. Another strategy is to utilize SSH port-sending to make a scrambled channels for the correspondence.
 Key Points
Key Points
- MySQL Security - Are the privilege measures that are taken as a part of the database.